
December 2020 Edition!
AIU News + Essays + Education + Culture + Science + Technology + Art + Design + Body + Mind + Spirit + Environment + Human Rights Master of Sociology + About AIU

AIU News + Essays + Education + Culture + Science + Technology + Art + Design + Body + Mind + Spirit + Environment + Human Rights Master of Sociology + About AIU
 October 20,
2020. Many
of you know
Dr. Rosa
Hilda Lora as
an Academic
Advisor
with AIU but did you know
she is also a columnist for the
newspaper El Siglo? Dr. Lora
has shared with us 3 of her
latest newspaper publications (in Spanish) that are very
analytical and of social benefit
to everything we live in. Read
her publications here: The
strength of the peoples:
October 20,
2020. Many
of you know
Dr. Rosa
Hilda Lora as
an Academic
Advisor
with AIU but did you know
she is also a columnist for the
newspaper El Siglo? Dr. Lora
has shared with us 3 of her
latest newspaper publications (in Spanish) that are very
analytical and of social benefit
to everything we live in. Read
her publications here: The
strength of the peoples:
 October 23,
2020. One of
our students,
Pablo Javier
Chami, will be
hosting a free
event via Eventbrite that he
created on: An Entrepreneurial
Tour, where he will serve
as the event manager
and mentor.
During this
special event,
he invites and
encourages entrepreneurs
from
different parts
of the world to converge in the same desire:
carry out ventures and create
a networking space.
Currently he is the Director
of the Center of Entrepreneur’s
UTNBA for last 12 years
and is studying a Bachelor’s
degree with a major in Business
at AIU.
October 23,
2020. One of
our students,
Pablo Javier
Chami, will be
hosting a free
event via Eventbrite that he
created on: An Entrepreneurial
Tour, where he will serve
as the event manager
and mentor.
During this
special event,
he invites and
encourages entrepreneurs
from
different parts
of the world to converge in the same desire:
carry out ventures and create
a networking space.
Currently he is the Director
of the Center of Entrepreneur’s
UTNBA for last 12 years
and is studying a Bachelor’s
degree with a major in Business
at AIU.
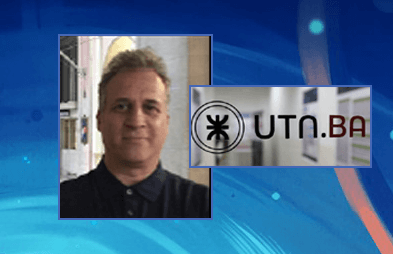
 November, 2020. These graduate students completed the majority
of the requirements to obtain honors, which included a 4.0
GPA, published works, recommendation from their respective
advisors, patent a product, etc. Congratulations!
November, 2020. These graduate students completed the majority
of the requirements to obtain honors, which included a 4.0
GPA, published works, recommendation from their respective
advisors, patent a product, etc. Congratulations!
 November
1, 2020. One
of our graduates,
Ambrues
Nebo, has published his
second book titled, The wave
of protests leading to regimes
change in Africa: a sociological
perspective, and it is available
on Amazon.
Summary: “Recently the
wave of social protests aiming
at regimes change in the global
community have been unprecedented
in scope. Africa having succeeded in stamping out the
tides of coup d'état, that over
the years undermined its growing
democracy, the continent
has now become a hub for the
momentous wave of social
protests that in less than a decade
changed four regimes and
making its way in other parts of
Africa. ...” Find his published
book here:
https://www.amazon.co.uk/dp/9975153461
Ambrues Nebo has completed
a Doctorate program in
Sociology at AIU.
November
1, 2020. One
of our graduates,
Ambrues
Nebo, has published his
second book titled, The wave
of protests leading to regimes
change in Africa: a sociological
perspective, and it is available
on Amazon.
Summary: “Recently the
wave of social protests aiming
at regimes change in the global
community have been unprecedented
in scope. Africa having succeeded in stamping out the
tides of coup d'état, that over
the years undermined its growing
democracy, the continent
has now become a hub for the
momentous wave of social
protests that in less than a decade
changed four regimes and
making its way in other parts of
Africa. ...” Find his published
book here:
https://www.amazon.co.uk/dp/9975153461
Ambrues Nebo has completed
a Doctorate program in
Sociology at AIU.
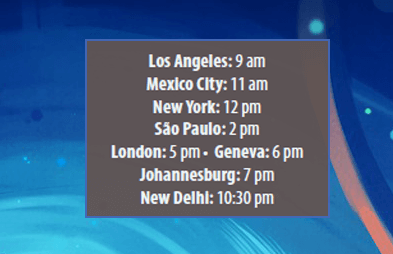 Human rights
vs XXI Century
challenges
International virtual conference
held in celebration of the
International Human Rights Day
Human rights
vs XXI Century
challenges
International virtual conference
held in celebration of the
International Human Rights Day

| Edson Fortunato e Silva da Costa Bache lor of Business Administration Business Administration Angola |
Angel Augusto Roggiero Doctor of Education Education Argentina |
Daniel Andrés Gómez Master of History Contemporary History of Asia Argentina |
Alberto Benítez Reynoso Post-Doctorate of Science Structural and Geotechnical Engineering Bolivia |
Eletsang Jeremiah Master of Science Information Systems Management Botswana |
Obakeng Sekaba Bache lor of Business Manageme nt Business Management Botswana |
| Ndam Blaise Tita Bache lor of Science Public Health Came roon |
Ansu Keifala Master of Science Petroleum Engineering Canada |
Metkel Zerai Abraham Bache lor of Economics Renewable Energy Canada |
Rashid Abdur Master of Business Administration Acc ounting Canada |
Maria de Lourdes Gomes Soares Bache lor of Science Health Sciences Cape Verde |
Mónica Carolina Acosta Zambrano Doctor of Science Information Technology Chile |
| Jaenrika Cloete Bache lor of Science Bacteriology China |
Diego Andrés Galván Triana Bache lor of Science Civil Engineering Colombia |
Angela Vivian Moreno Córdoba Bache lor of Science Nutrition and Dietetics Colombia |
Ana María Muñoz Monroy Bache lor of Science Architecture Colombia |
Sumo Jallah Master of Business Administration Supply Chain and Logistics Management Dem ocratic Rep ublic of Congo |
Hilaire Nsabala Mbwolie Doctor of Science Public Health Dem ocratic Rep ublic of Congo |
| George Báez José Master of Education Education Dominican Rep ublic |
Maximilia Peña Regalado Bache lor of Education Education Dominican Rep ublic |
Pablo Tomas Mancebo García Doctor of Science Public Health Dominican Rep ublic |
Ramona Cristina Zabala Sosa Doctor of Linguistics Semiotics and Polysemy Dominican Rep ublic |
Nantip Gabriel Chuint Nunkui Master of Science Education Ecuador |
Guayasamín Juan Carlos Doctor of Business Administration Project Management Ecuador |
| Samy Mohamed Sayed Ibrahim Master of Business Administration Hospitality Management Egypt |
Carlos Alberto Carcach Alfaro Doctor of Philosoph y Criminology El Salvador |
Juanita Nsue Bacale Bache lor of Marke ting Marketing and Administration Equatorial Guinea |
Natividad Ondo Bindang Bache lor of Finance and Banking Finance and Banking Equatorial Guinea |
Curlan Joseph Gilchrist Doctor of Philosoph y Economics Grenada |
Maria Eugenia del Rosario Tabarini Soto Master of Social Work Marriage and Family Therapy Guatem ala |
| Yeimy Xiomara Muñoz Rodríguez Bache lor of Business Administration Business Administration Guatem ala |
Manuel de Jesus Puerto Castellanos Doctor of Economics Economics Honduras |
Karen Akwuobi Doctor of Science Clinical Psychology Ireland |
Olugbenga O. Agbolade-David Doctor of Philosoph y English Language and Linguistics Ireland |
Durgham Jamal Khalil Doctor of Philosoph y Education Administration Israel |
Stefania Allegra Doctor of Philosoph y Management Education and Business Mgmt. Italy |
| Maxine Patricia Wilson Doctor of Business Administration Business Administration Jamaica |
Mark Michiera Mandare Bache lor of Science Civil Engineering Kenya |
Retselisitsoe Ratikoane Bache lor of Science Public Health Lesotho |
Benson Malunga Phiri Master of International Relations International Relations Malawi |
Djakalia Koné Master of Supp ly Chain Manageme nt Supply Chain Management Mali |
Marcos Daniel Venegas Caldera Doctor of International Relations International Relations and Globalization Mexico |
| Ben A. G. Bambo, Sr. Doctor of Philosoph y Global Health Education Micronesia |
Arnaldo Fernando Nhavene Doctor of Business Business Management Mozambique |
Winsome May Saldanha Post-Doctorate of Science Chemistry Myanmar |
Dorcas Jeruto Chepkwony Bache lor of Science Tourism Management Nethe rlands |
Ejetavwo Mukoro Bache lor of Science Chemical Engineering Nigeria |
Bashir Saleh Haladu Bache lor of Arts Acc ounting Nigeria |
| Steven Puwase Enore Master of Business Administration Business Administration Papua New Guinea |
Alfred Tolaget Associate of Science Electrical Engineering Philipp ines |
Muhire Simon Charles Doctor of Philosoph y Leadership and Governance Rwanda |
Igabe Egide Doctor of Science Financial Engineering and Industrial Sys. Rwanda |
Raphala Mahlodi Asnath Master of Education Education Technology South Africa |
Peter Okonkwo Master of Philosoph y Psychology St. Vincent & Grenadines |
| Lilas Adnan Tomeh Doctor of Philosoph y Public Health Syria |
Juan Augusto Peña Kujath Bache lor of Science Aeronautical Engineering USA |
Jameelah P. Blackwell-Phills Doctor of Education Education USA |
Franco Egbe Master of Science Civil Engineering USA |
Ben Leonards Okello Doctor of Arts Miss iology USA |
Kassem El Saad Doctor of Human Rights Human Rights USA |
| Sidney Kabwe Bache lor of Science Human Biology Zambia |
Chikambi Ntokwa Doctor of Philosoph y Business Administration Zambia |
William K. Mutomba Master of Biblical Studies Biblical Studies Zimbabwe |
Ignatius Chakavarika Master of International Relations International Relations Zimbabwe |
||
 Tilahun Zaga
Tilahun Zaga
 Lavile Guilavogui
Lavile Guilavogui
 Telesia Musili
Telesia Musili
 Victor Caxton Odadah
Victor Caxton Odadah
Research indicates that the
high rate of cybercrime
results from carelessness as
private industries and individuals
underestimate the risk
of cybercrime and therefore
fail to take adequate measures
to protect their information
and sensitive data. In addition,
over dependence by the
government on centralized
systems and lack of proper
guidelines on protecting personal
information contained
in these systems has left
millions of individual sensitive
information vulnerable.
In response to the increased
cases of cybercrime, governments
are investing millions of
dollars in building cyber skill and capability to as a cybercrime
prevention measure
(Dashora, 2011). Other scholars
have focused on the way
cybercrime influences other
issues in the modern society.
For instance, Fatima (2015)
explores the way cybercrime
influences the practices in
the apparent modern niche of
E-Banking. Fatima explores
the trends, the threats and
the strategies of combating
cybercrime in the E-Banking
niche while also investigating
the potential of biometrics in
addressing cybercrime in the
E-Banking niche.
An investigation
on the way cybercrime
influences the victimization of
women has also been conducted
(Halder & Jaishankar, 2012).
The authors explore the various
circumstances in which
women have been victimized
through cybercrime attacks.
Nelson, Phillips and Stuart
(2014) have developed a guide
to computer forensics and investigations.
The authors point
out to the past trends, the current
initiatives and the future
projections on the way computer
crime and investigations should be undertaken. Poole
and Sky-Mcllvain (2014)
explore the current trends and
recommend the way education
should be undertaken in
the modern age. Weisburd and
McEwen (2015) recommend
the way cybercrime should
be mapped with the aim of
developing and implementing
strategies that will deter
cybercrime. Stephenson and
Gilbert (2013) offer a guide on
the way cybercrime investigations
should be undertaken.
From the analysis of all the
literature cited in the paper,
it is apparent that there are
strategies that work, and
others that are ineffective
in deterring and combating
cybercrime challenges now
and into the future (Putnam &
Elliott, 2001).
Viruses form the highest
negative influence on users
in relation to cybercrime.
Majority of the internet users
report viruses as their main
threat as compared to the
number of people who report
losing money in a survey
conducted in 2012 and 2013
(McGuire,2013). Similarly, businesses report virus related
problems as their main
threat on security incident.
The samples were collected
through random sampling.
Statistics from police recordings
on cybercrime on police
department show that fraud
as the most reported form
of cybercrime. However, the
data presented from the police
cases is not separated into
online and offline therefore
making the information hard
to analyze. These presented
the main challenge of conducting
research-using data
provided by the police. For
instance, the police were more
likely to record computers
fraud as cybercrime without
indicating if the crime was
committed online or offline
(McGuire, 2013).
Majority of the research on
cybercrime prevention are
based on review of relevant
literature and lack of adequate
information on the field is one
of the biggest challenges. Secondly,
much of the information
is obtained from self-reports
which as indicated earlier
has the challenge on existent
laws under which cybercrime
is reported. Limited data on
cybercrime and the emerging
forms of such crimes as
cyber terrorisms is the greatest
weakness of various researches
on cyber-crime prevention. In
addition, the survey questions
that are mostly used in the
conducting these researches
are self-selecting which implies
that the information collected
is limited in relation to the
actual cybercrime. Similarly,
most of the crimes are under
reported by the victims and
organizations due to the fear of
negative publicity. Therefore,
the actual information relating
to cybercrime is withheld
by the victims, which greatly
hinders finding an effective
solution to the problem (Rotich
et al, 2014).
Several modes are suggested
to help reduce increasing
rate of cybercrime. One is
the KVIRUS model, which is a
virus prevention model that
aim at identifying virus according
to their programs rather
than software signature. Other
models aim at identifying the
cybercriminal through using
the details of the internet service
Provider ISP and use the
necessary laws to apprehend
the criminal. However, with the
current technology advancement,
this is proving a little bit
difficult as criminal have come
with programs to avoid being
detected (Rotich et al, 2015).
The current study purposively
selected cybercrime policies
formulated by the United
States to address cybercrime.
The sampling criteria was Influenced
by the scope covered
by the policy, the resources required to implement the
policy effectively and reported
statistics related to the
problem that the policy aims
to address. Various resources
that included presidential
orders, state and federal laws
and regulations were used
as the primary data sources
for analysis. The analysis
evaluated existing policies
to determine their ability in
covering their intended goals.
The study focused on the
weakness and strengths of the
undefined policies evaluating
their flaws in curbing the
rising threat of cybercrime.
Although much of policies
were worked during the time
they were implemented, the
emerging trends in cybercrime
have made them ineffective
or useless. The study therefore
adopted the policy analysis
methodology to identify the
flaws in the selected polices
and recommending possible
changes that can be adopted
to ensure that the policies are
effective in combating the
rising threat of cybercrime
through multi-goal policy
analysis approach.
The multi-goal policy analysis
approach involves selecting
the impact of the goals of the
policy analyzed. The goals are
identified and accessed if they
meet the desired objectives set
by the policymakers (Weimer &
Vining, 2005). Next is predicting
the impact that is expected
with the modifications of the
policy to achieve the relevant
goals. The predicted impact
from the policy modifications
is valued as well as evaluating
the modifications that
are suggested for the policy.
The current study focuses on
understanding the current
polices on cybercrime through
evaluating their strength and
weakness to recommend necessary
changes that can make
them more effective. The current
study therefore involved
gathering the information
on the selected policies and analyzing to identify the problems
facing the policies and
recommended changes.
Recommendations
Based on the findings of the
analysis done by the current
study, it is recommended that
the computer and abuse act
should therefore be amended
to include all the computers
that are in the risk of cybercrime
attacks. The act only
covers protected computers
which include government
and financial institutions
computers (Jarrett & Bailie,
2015). Non –financial institutions
and other organizations
not covered under the
protected computer provision
of the CFAA act are incurring
millions in losing due to unauthorized
access to information
and data by cyber criminals.
In addition, criminal activities
on non-protected computers
give the criminals an advantage
to test various tools and
software through which they
can employ on protected computers
more easily. Similarly,
to the computer abuse act,
the study recommends that
the information intercept act
should be amended to include
the broad acts of criminal
activities committed on nonprotected
computers. Private
organizations computers hold
sensitive information that
although not directly related
to state matters, its disclosure
can have an indirect impact to
critical infrastructure. Based
on the study findings, it is
also recommended that the
government should amend the
identity theft clause to include
criminals who use identities
of people who do not exist
currently, the provisions of the
law only ally to people who
falsify the identity of other
existent people as their own.
To discourage illegal access
to information and data on
providers of storage services,
the policy should be expanded
to include the illegal sharing
of information by the service
providers who have access of
such information as a cybercrime.
Cybercrime is unarguably
a complex challenge in
the modern world that is defined
by immense technological
undertakings. Therefore,
it is imperative that working
strategies are employed in
combating its threats. Based
on the findings on the study, it
is recommended that organizations
such as homeland
department of security develop
a case-specific approach
in developing tactics that will
prevent future repeats. The
department of homeland security
has adopted regulatory
procedures that focus on the
parties at the risk of experiencing
cyber-attacks and doing
away with the focus on the
groups that initiate cybercrime
attacks which is proving an
effective measure reduce cybercrime
attacks (Department
of Homeland Security, 2015).
Lastly, organizations should
set aside investment that
will fund research activities
to determine the fronts that
make it easier for perpetrators
to initiate cybercrime attacks.
The study also recommends
that organizations implement
both technological measures
such applying latest security
patches, up to date antivirus,
operating systems and computer
application, password
protection, maintaining a
strict validation for the data
input, monitoring the processes
as well as procedures
of external contractors who
have access to the organizations
computer systems.
Others include performing
regular scans to the network
securities and activities, and
create awareness on cybercrime
prevention among their
employees. This will create an
environment where everyone
is cautious of the rising thereat
on preventing cybercrime.
The United States congress
should increase the resources
and the funding to fighting
cybercrime. the government
allocated $14 billion in the 2016
year to cyber security and
plans to increase this by 35% to
$19 billion in the coming 2017
budget (The White House,2016).
This is essential as cybercrime
criminals are organizing
themselves in forms of groups
and outsourcing funding from
terrorist groups and other
criminal’s organizations to advance
their criminal activities.
With the potential to utilize
modern technologies in facilitating
cybercrime, the extent
of the damages caused by such
actions has therefore increased.
The government should also
increase the capacity of its
agencies ad department the
fight with cybercrime through
more resource allocations, provision of relevant training
and skills in handling the crisis.
Similarly, the information sharing
policies from the presidential
directives on cybercrime
can be very effective in combating
the threat of cybercrime
if well enacted. However, the
policies are very ambiguous
as currently constituted and
require comprehensive reforms
to ensure they are easily
implemented and workable.
For instance, the provision on
information sharing is currently
limited by the existing legal
barriers on information sharing
between the government and
the private sectors.
The study also recommends
the establishment of a specific
national agency that will coordinate
efforts of preventing
cybercrime, its mitigation and
prosecution just like the case
with the drugs. The agency
should comprise of top strategic,
business and technical
thinkers outside the government.
The agency will push for
proposals and recommendations
on the effective legislations
and actions to combat
cybercrime through enhancing
cyber security awareness,
maintaining the security of
the private and government
sectors and empowering
the American public to take
charge of their digital security.
Currently, cybercrime handled
by the DHS and other federal
agencies which include the
FBI, the US Secret Service and
US Immigrations and Customs
Enforcement (ICE) which
have been assigned other
responsibilities by the federal
government (Department of
Homeland Security, 2016).
Such an agency should focus
on creating a good working relationship
between the private
and the government sectors
especially in combating
cybercrime. The government
should also embrace creating
awareness through education
and training to provide the
public with accurate, consistent
and reliable information
on cybercrime. The department
of Homeland Security
that currently coordinates
cybercrime prevention efforts
should increase training and
awareness initiatives for the
public sector. Other initiatives
include creating an effective
cyber workforce that is responsible
for ensuring cyber
security through enforcing the
enacted legislations in combating
cybercrime.
The End
BIBLIOGRAPHY.
Bessant, J. (2014). Democracy Bytes: New Media, New Politics
and Generational Change. Springer. • Broadhurst, R., Grabosky, P., Alazab, M.,
Bouhours, B., & Chon, S. (2014). An Analysis of the Nature of Groups Engaged in
Cyber crime. An Analysis of the Nature of Groups engaged in Cyber crime, International
Journal of Cyber Criminology, 8(1), 1-20. • Brown, C. S. (2015). Investigating
and prosecuting cyber crime: forensic dependencies and barriers to justice.
International Journal of Cyber Criminology, 9(1), 55. • Bucci, S. P., Rosenzweig,
P., & Inserra, D. (2013). A congressional guide: Seven steps to US Security, Prosperity,
and Freedom in Cyberspace.Heritage Foundation Backgrounder, (2785).
• Byrne, J., & Marx, G. (2011). Technological innovations in crime prevention
and policing. A review of the research on implementation and impact. Journal
of Police Studies, 20(3), 17-40. • Casey, E. (2011). Digital evidence and computer
crime: Forensic science, computers, and the internet. Academic press. • Choo,
K. K. R. (2011). The cyber threat landscape: Challenges and future research directions.
Computers & Security, 30(8), 719-731. • Choudhury, R. R., Basak, S., &
Guha, D. (2013). Cyber Crimes-Challenges & Solutions. International Journal of
Computer Science and Information Technologies, 4(5). • Clarke, R., Dempsey,
G., Ooi, C. N., & O'Connor, R. F. (1998, February). Technological Aspects of Internet
Crime Prevention'. In Proc. Conf.'Internet Crime', Australian Institute for
Criminology, Melbourne University (pp. 16-17). • Dashora, K. (2011). Cyber crime
in the society: Problems and preventions. Journal of Alternative Perspectives in
the Social Sciences, 3(1), 240-259. • Department of homeland security. (2015). Using
the Cybersecurity Framework | Homeland Security. Retrieved from https://
www.dhs.gov/using-cybersecurity-framework# • Department of Homeland
Security. (2016). Combating Cyber Crime | Homeland Security. Retrieved from
https://www.dhs.gov/topic/combating-cyber-crime • Department of Justice.
(2015). Computer Crime and Intellectual Property Section (CCIPS) | Department
of Justice. Retrieved from https://www.justice.gov/criminal-ccips • Fatima, A.
(2015). E-Banking Security Issues? Is There A Solution in Biometrics?. The Journal
of Internet Banking and Commerce, 2011. • Federal Trade commision. (2008).
CAN-SPAM Rule | Federal Trade Commission. Retrieved from https://www.ftc.
gov/enforcement/rules/rulemaking-regulatory-reform-proceedings/can-spamrule
• Federal Trade Commission. (1998). Identity Theft and Assumption Deterrence
Act | Federal Trade Commission. Retrieved October 9, 2016, from https://
www.ftc.gov/node/119459 • Halder, D., & Jaishankar, K. (2012). Cyber crime and
the victimization of women: laws, rights and regulations. Information Science
Reference. • Jarrett, M., & Bailie, M. (2015). Prosecuting Computer Crimes. Office
of Legal Education Executive Office for United States Attorneys. Retrieved from
https://www.justice.gov/sites/default/files/criminal-ccips/legacy/2015/01/14/
ccmanual.pdf • McMahon, R., Serrato, D., Bressler, L., & Bressler, M. (2015).
Fighting cyber crime calls for developing effective strategy. Journal of Technology
Research, 6, 1. • McQuade, S. C. (2006). Understanding and managing cyber
crime. Boston: Pearson/Allyn and Bacon.
A part of this globalized society
lived very happy because
they said to themselves:
we have already achieved
everything, there’re no limits
to trade, people travel everywhere
and communication is
instantaneous. What more can
you ask of this world?
We were still in the mad
rush of global commerce and
instant communication.
A new virus comes to us and
many, among rulers and part
of the population, thought that
with the power of this new
society, that would soon end.
But Oh Surprise of surprises!
The virus is in its
second wave in Europe and
this humanity with so much
science and technology can’t
with such a small being.
Confinements are heard: in
some countries severe, in others,
recommendations, but all
to continue without being able
to do the previous life.
There is also a wave of
protests because we have a
life created for commerce:
large centers to watch sporting
events, also large shopping
centers, cinemas, bars, restaurants,
but we are seeing that
people no longer know how to
make a life only at home.
And what is our pending assignment
or subject in the face
of so much abundance?
On the contrary, another
part of the inhabitants of our
planet said: a development in
this way can’t be possible or
sustainable. We have forgotten
that abundance is for the
few; 10% of the population
owns the world’s wealth.
We are at a point of reflection:
we change or we change.
Our pending assignment is:
The Biosphere.
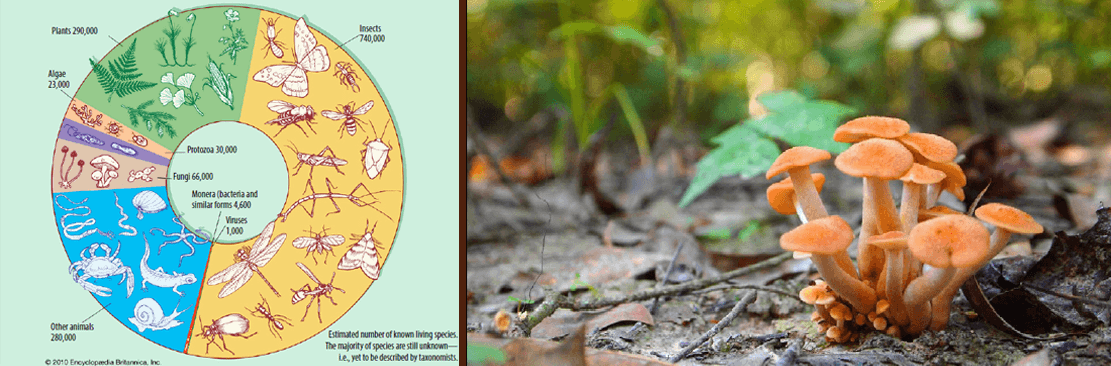
The Biosphere comprises
the life that surrounds the
Earth.
The life that surrounds the
Earth is made up of:
· The flora
· The fauna
Human beings necessarily
contribute and participate in
that life that surrounds the
Earth. When we speak about
Biosphere we refer to the
Global Ecosystem. The concept
of Ecosystem arises with Arthur Tansley in 1935.
This wonderful world, in
this stage of Capitalism or
Globalization, was made
with a development that only
prevailed: obtaining resources
from wherever it was without
thinking about whether
they were renewable or not,
without measuring the consequences
of all the changes that
were made.
There are some countries
that need 7 planets Earth to
continue their production
career. We reserve names for
professional ethics for people
born in those countries who
will surely feel bad for what
they are not guilty of.
What is the Biosphere? What
have we done with it? Our
global Ecosystem formed by
the balance of what constitutes
our planet Earth, speaking
about flora, fauna and
terrestrial constitution, has a
balance that allows it to exist.
This balance is maintained
within a system that receives external elements which need
to self-regulate in order for it
to be sustained.
About our planet and its
existence we have the Gaia
hypothesis, now Theory, by
James Lovelock that considers
the Earth as a living being
that is maintained, that needs
the balance of all the elements
that exist in it. Here comes
the Second Law of Thermodynamics
and the self-regulation
of systems, which Ilyia
Prigogine very well details in
his work, Just an illusion?
The Lovelock equilibrium
and the Prigogine equilibrium don’t refer to a system where
everything is stable; it refers to
elements that enter the system
and those that leave, maintaining
stability.
According to Prigogine: “Our
age is characterized, more than
any other, by a growing diversification
of knowledge, techniques
and modes of thought.
However, we live in a unique
world in which each area
involves the others; for this
reason I consider it essential to
clarify certain concomitants”.
(Prigogine 2009, p. 47)
What is happening with our
planet today?
With the flora and the
development of commerce
in Globalization, vegetation
is eliminated because in this
place we are going to build
a residential or commercial
development or whatever
we want and the life of all
vegetation in that space is
eliminated.
The same thing happens
with the Fauna. If we
remove all vegetation from a
space, the animals that lived
there have to find another area
to live if they have not already
been killed.
Nowadays, the human beings,
faced with the spread of
the coronavirus, have had to
confine themselves to their
homes, we see animals walking
in the streets: our enemies,
human beings, it seems they
disappeared. Yes, there is a
self-regulation of the life system,
what is happening today
is that we have passed the
limits in which it can maintain
balance, so we see organizations
and organizations looking
for ways for human beings
to maintain the necessary
balance for life.
The United Nations Educational,
Scientific and Cultural
Organization (UNESCO), has
the 2030 Agenda for Sustainable
Development.
Nowadays we see countries
that in the face of deforestation
caused by urban developments
are creating green areas on the
roofs, for example England in
London. Human beings are
destroying the global ecosystem
and now what it follows is
the violence against each other.
Everywhere we are seeing acts
of violence by some human
beings against others.
What else is missing from
our planet Earth?
According to Lovelock, the
coronavirus exists because
the human being has created
elements that allow the virus
to live.
We have a pending assignment
Educate ourselves to make a
world possible.
• Educate ourselves for the life of
all beings also considering the
life of our planet.
• We can do it but we must want
to do it.
• We say that we are rational beings,
but violence means lack of reasoning;
I get this by generating fear
in others.
• Life must be: our life, the life of others
and the life of the planet; in each
one this is our pending assignment
BIBLIOGRAPHY. Lovelock, J. Entrevista.- Español – Julio 19- 2020. Retrieved from: https://www.climaterra.org/post/
lovelock-la-biosfera-y-yo-estamos-en-el-%C3%BAltimo-1-de-nuestras-vidas | Lovelock, J. – Original Interview- English - July
18- 2020- Retrieved from: https://www.theguardian.com/environment/2020/jul/18/james-lovelock-the-biosphere-and-i-are-both-inthe-
last-1-per-cent-of-our-lives | Lovelock, J. Gaia, una nueva visión de la vida sobre la Tierra. Retrieved from: http://
mateandoconlaciencia.zonalibre.org/gaia.pdf | Lovelock, J.- Gaia. Retrieved from: https://www.youtube.com/watch?v=GIFRg2skuDI
| Organización de las Naciones Unidas para la Educación, la Ciencia y la Cultura (UNESCO), Página Oficial.
Retrieved from: https://es.unesco.org/about-us/introducing-unesco | Prigogine, I. (2009). ¿Tan solo una ilusión?. Barcelona:
Tusquest Editores. | UNESCO – AGENDA 2030 - DESARROLLO SOSTENIBLE. Retrieved from: https://es.unesco.org/
sdgs | UNESCO – Objetivos de Desarrollo Sostenible. Retrieved from: https://es.unesco.org/sdgs
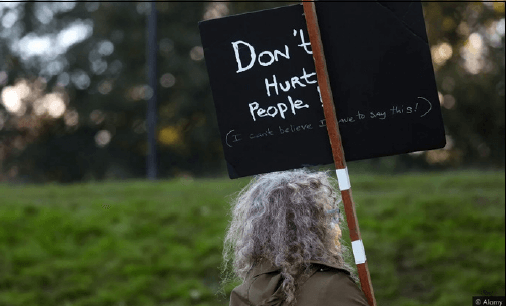 Inflicting harm or pain on someone
incapable of doing the same to you
might seem intolerably cruel, but it
happens more than you might think.
... We understand if someone lashes
out in retaliation or self-defence. But
when someone harms the harmless,
we ask: “How could you?”
Humans typically do things to get
pleasure or avoid pain. For most of
us, hurting others causes us to feel
their pain. And we don’t like this feeling.
This suggests two reasons people
may harm the harmless –either they
don’t feel the others’ pain or they
enjoy feeling the others’ pain. Another
reason people harm the harmless
is because they nonetheless see a
threat. Someone who doesn’t imperil
your body or wallet can still threaten
your social status. This helps explain
otherwise puzzling actions ... Liberal
societies assume causing others to suffer
means we have harmed them. Yet
some philosophers reject this idea. ...
Someone who gets pleasure from
hurting or humiliating others is a
sadist. Sadists feel other people’s
pain more than is normal. And they
enjoy it. ... The everyday sadist may
be an internet troll or a school bully.
... Unlike sadists, psychopaths don’t
harm the harmless simply because
they get pleasure from it (though
they may). Psychopaths want things.
If harming others helps them get ...
Read full text:
Inflicting harm or pain on someone
incapable of doing the same to you
might seem intolerably cruel, but it
happens more than you might think.
... We understand if someone lashes
out in retaliation or self-defence. But
when someone harms the harmless,
we ask: “How could you?”
Humans typically do things to get
pleasure or avoid pain. For most of
us, hurting others causes us to feel
their pain. And we don’t like this feeling.
This suggests two reasons people
may harm the harmless –either they
don’t feel the others’ pain or they
enjoy feeling the others’ pain. Another
reason people harm the harmless
is because they nonetheless see a
threat. Someone who doesn’t imperil
your body or wallet can still threaten
your social status. This helps explain
otherwise puzzling actions ... Liberal
societies assume causing others to suffer
means we have harmed them. Yet
some philosophers reject this idea. ...
Someone who gets pleasure from
hurting or humiliating others is a
sadist. Sadists feel other people’s
pain more than is normal. And they
enjoy it. ... The everyday sadist may
be an internet troll or a school bully.
... Unlike sadists, psychopaths don’t
harm the harmless simply because
they get pleasure from it (though
they may). Psychopaths want things.
If harming others helps them get ...
Read full text:
 Americans are leaving the country
or seeking foreign visas in record
numbers, according to immigration
lawyers and expatriate organizations,
during an oppressive year of political
violence, racial strife and an uncontrolled
pandemic that has kept families
locked in their homes for months —
with no clear end in sight.
The exodus has been led by parents
looking for countries with open
and safe schools and by members
of marginalized groups fed up with
institutionalized racism, shaken by
the visibility of white supremacists
and worried about what a Supreme
Court swing to the right will mean
for their civil liberties. They’re largely
Americans with financial means and
the ability to work virtually, and some
are dual citizens and their spouses. ...
The number of Americans who were
recorded as having given up their
citizenship or U.S. residency soared to
5,816 in the first six months of 2020,
compared with 2,072 in all of 2019,
according to data from the Internal
Revenue Service. In the third quarter,
the numbers dropped dramatically to
about 800, as embassies curbed services
because of the pandemic. ...
Read full text:
Americans are leaving the country
or seeking foreign visas in record
numbers, according to immigration
lawyers and expatriate organizations,
during an oppressive year of political
violence, racial strife and an uncontrolled
pandemic that has kept families
locked in their homes for months —
with no clear end in sight.
The exodus has been led by parents
looking for countries with open
and safe schools and by members
of marginalized groups fed up with
institutionalized racism, shaken by
the visibility of white supremacists
and worried about what a Supreme
Court swing to the right will mean
for their civil liberties. They’re largely
Americans with financial means and
the ability to work virtually, and some
are dual citizens and their spouses. ...
The number of Americans who were
recorded as having given up their
citizenship or U.S. residency soared to
5,816 in the first six months of 2020,
compared with 2,072 in all of 2019,
according to data from the Internal
Revenue Service. In the third quarter,
the numbers dropped dramatically to
about 800, as embassies curbed services
because of the pandemic. ...
Read full text:
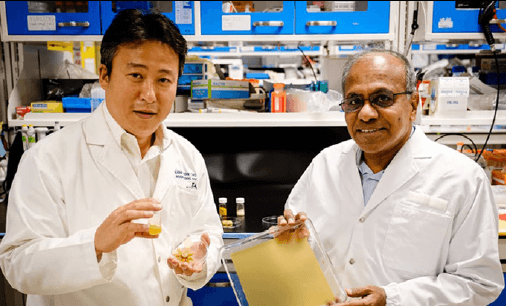 Scientists at Singapore’s Nanyang
Technological University (NTU
Singapore) have transformed the ultratough
pollen grains from sunflowers
into a pliable, gel-like material through
a process similar to conventional
soap-making. By casting this gel-likee
material into a mold and left to dry,
scientists successfully created paperlike
material.
This paper-like material can bend
and curls with changing levels of
environmental humidity. What’s more,
its mechanical properties may make it
useful for a wide range of applications
such as soft robots, sensors, artificial
muscles, and electric generators.
In the study, scientists
demonstrated that material’s properties
could be altered using a strip of
pollen-based paper that can ‘walk.’
NTU Professor Cho Nam-Joon, who
holds the Materials Research Society
of Singapore Chair in Materials Science
and Engineering, said: “These
findings build on the recent work by
our NTU team, in which we showed
how hard pollen grains could be
converted into soft microgel particles
that alter their properties in response
to external stimuli. This process also
renders pollen and the products we
create from it, non-allergenic.” ...
Scientists at Singapore’s Nanyang
Technological University (NTU
Singapore) have transformed the ultratough
pollen grains from sunflowers
into a pliable, gel-like material through
a process similar to conventional
soap-making. By casting this gel-likee
material into a mold and left to dry,
scientists successfully created paperlike
material.
This paper-like material can bend
and curls with changing levels of
environmental humidity. What’s more,
its mechanical properties may make it
useful for a wide range of applications
such as soft robots, sensors, artificial
muscles, and electric generators.
In the study, scientists
demonstrated that material’s properties
could be altered using a strip of
pollen-based paper that can ‘walk.’
NTU Professor Cho Nam-Joon, who
holds the Materials Research Society
of Singapore Chair in Materials Science
and Engineering, said: “These
findings build on the recent work by
our NTU team, in which we showed
how hard pollen grains could be
converted into soft microgel particles
that alter their properties in response
to external stimuli. This process also
renders pollen and the products we
create from it, non-allergenic.” ...
 The body’s tissues routinely communicate
with each other through RNA
messages sent back and forth between
cells. So, it seemed obvious to scientists
that, by eavesdropping on these extracellular
communiqués carried in blood,
saliva, urine and other fluids, they
should be able to intercept dispatches
indicative of health and disease.
If only it were that easy. “When
people got into this, we were all a bit
naive,” says Louise Laurent, a perinatologist
at the University of California,
San Diego (UCSD). Laurent is one of a
growing number of scientists trying to
develop minimally invasive RNA tests
for the early detection and clinical
management of cancer, heart disease,
neurodegeneration and other ailments.
But the inherent diversity of extracellular
RNA (exRNA) molecules, and the
packages that transport them, poses a
considerable challenge. “I don’t think
anybody expected the complications
of the biology,” says Laurent, whose
own research focuses on using exRNA
to predict complications in pregnancy.
Heterogeneity of the RNA repertoire
can make it difficult to discern
clinically useful biomarkers amid the
background molecular noise. And then,
to confound matters further, all sorts of
technical challenges ...
The body’s tissues routinely communicate
with each other through RNA
messages sent back and forth between
cells. So, it seemed obvious to scientists
that, by eavesdropping on these extracellular
communiqués carried in blood,
saliva, urine and other fluids, they
should be able to intercept dispatches
indicative of health and disease.
If only it were that easy. “When
people got into this, we were all a bit
naive,” says Louise Laurent, a perinatologist
at the University of California,
San Diego (UCSD). Laurent is one of a
growing number of scientists trying to
develop minimally invasive RNA tests
for the early detection and clinical
management of cancer, heart disease,
neurodegeneration and other ailments.
But the inherent diversity of extracellular
RNA (exRNA) molecules, and the
packages that transport them, poses a
considerable challenge. “I don’t think
anybody expected the complications
of the biology,” says Laurent, whose
own research focuses on using exRNA
to predict complications in pregnancy.
Heterogeneity of the RNA repertoire
can make it difficult to discern
clinically useful biomarkers amid the
background molecular noise. And then,
to confound matters further, all sorts of
technical challenges ...
 While the US flounders in its
response to the coronavirus,
another nation —one within our own
borders— is faring much better.
With a mask mandate in place since
spring, free drive-through testing,
hospitals well-stocked with PPE, and
a small army of public health officers
fully supported by their chief,
the Cherokee Nation has been able
to curtail its Covid-19 case and death
rates even as those numbers surge in
surrounding Oklahoma, where the
White House coronavirus task force
says spread is unyielding.
Elsewhere in the US, tribal areas
have been hit hard by the virus. The
Centers for Disease Control and Prevention
reports that American Indian
and Alaskan Native populations have
case rates 3.5 times higher than that
of white individuals. The Navajo
Nation, where Covid testing, PPE,
and sometimes even running water
are in short supply, has seen nearly
13,000 cases and 602 deaths among
its roughly 170,000 citizens. The
Cherokee Nation, with about 140,000
citizens on its reservation in northeastern
Oklahoma, has reported just
over 4,000 cases and 33 deaths.
“It’s dire, but what in the world
would it look like if we weren’t doing
this work?’” said Lisa Pivec, senior
director of public health for Cherokee
Nation Health Services. ...
Read full text:
While the US flounders in its
response to the coronavirus,
another nation —one within our own
borders— is faring much better.
With a mask mandate in place since
spring, free drive-through testing,
hospitals well-stocked with PPE, and
a small army of public health officers
fully supported by their chief,
the Cherokee Nation has been able
to curtail its Covid-19 case and death
rates even as those numbers surge in
surrounding Oklahoma, where the
White House coronavirus task force
says spread is unyielding.
Elsewhere in the US, tribal areas
have been hit hard by the virus. The
Centers for Disease Control and Prevention
reports that American Indian
and Alaskan Native populations have
case rates 3.5 times higher than that
of white individuals. The Navajo
Nation, where Covid testing, PPE,
and sometimes even running water
are in short supply, has seen nearly
13,000 cases and 602 deaths among
its roughly 170,000 citizens. The
Cherokee Nation, with about 140,000
citizens on its reservation in northeastern
Oklahoma, has reported just
over 4,000 cases and 33 deaths.
“It’s dire, but what in the world
would it look like if we weren’t doing
this work?’” said Lisa Pivec, senior
director of public health for Cherokee
Nation Health Services. ...
Read full text:
 A nasal spray that blocks the absorption
of the SARS-CoV-2 virus
has completely protected ferrets it was
tested on, according to a small study
released on November by an international
team of scientists. The study,
which was limited to animals and has
not yet been peer-reviewed, was assessed
by several health experts at the
request of The New York Times.
If the spray, which the scientists
described as nontoxic and stable, is
proved to work in humans, it could
provide a new way of fighting the
pandemic. A daily spritz up the nose
would act like a vaccine.
“Having something new that works
against the coronavirus is exciting,” said
Dr. Arturo Casadevall, the chairman
of immunology at the Johns Hopkins
Bloomberg School of Public Health,
who was not involved in the study. “I
could imagine this being part of the
arsenal.” ... The team would require additional
funding to pursue clinical trials
in humans. ... The spray attacks the
virus directly. It contains a lipopeptide,
a cholesterol particle linked to a chain
of amino acids, the building blocks of
proteins. This particular lipopeptide exactly
matches a stretch of amino acids
in the spike protein of the virus, which
the pathogen uses to attach to a human
airway or lung cell. ...
A nasal spray that blocks the absorption
of the SARS-CoV-2 virus
has completely protected ferrets it was
tested on, according to a small study
released on November by an international
team of scientists. The study,
which was limited to animals and has
not yet been peer-reviewed, was assessed
by several health experts at the
request of The New York Times.
If the spray, which the scientists
described as nontoxic and stable, is
proved to work in humans, it could
provide a new way of fighting the
pandemic. A daily spritz up the nose
would act like a vaccine.
“Having something new that works
against the coronavirus is exciting,” said
Dr. Arturo Casadevall, the chairman
of immunology at the Johns Hopkins
Bloomberg School of Public Health,
who was not involved in the study. “I
could imagine this being part of the
arsenal.” ... The team would require additional
funding to pursue clinical trials
in humans. ... The spray attacks the
virus directly. It contains a lipopeptide,
a cholesterol particle linked to a chain
of amino acids, the building blocks of
proteins. This particular lipopeptide exactly
matches a stretch of amino acids
in the spike protein of the virus, which
the pathogen uses to attach to a human
airway or lung cell. ...
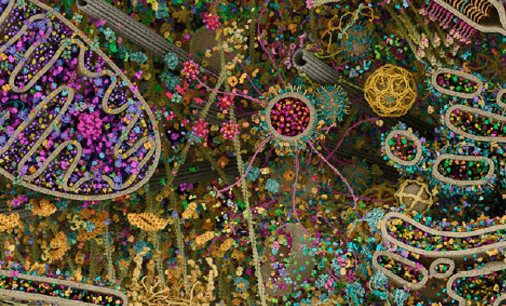 Created for Cell Signaling Technology, Inc., and inspired by the stunning art of David
Goodsell, this 3D rendering of a eukaryotic cell is modeled using X-ray, nuclear magnetic
resonance (NMR), and cryo-electron microscopy datasets for all of its molecular
actors. It is an attempt to recapitulate the myriad pathways involved in signal transduction,
protein synthesis, endocytosis, vesicular transport, cell-cell adhesion, apoptosis,
and other processes. ...
Created for Cell Signaling Technology, Inc., and inspired by the stunning art of David
Goodsell, this 3D rendering of a eukaryotic cell is modeled using X-ray, nuclear magnetic
resonance (NMR), and cryo-electron microscopy datasets for all of its molecular
actors. It is an attempt to recapitulate the myriad pathways involved in signal transduction,
protein synthesis, endocytosis, vesicular transport, cell-cell adhesion, apoptosis,
and other processes. ...
 Velvet Minnick, 44, is the owner
and head coach at 460 Fitness
in Blacksburg, Virginia. Like many
gym owners across the nation, she
was forced to shut down the facility
in March due to coronavirus. ... As the
state entered Phase 2 of reopening in
June, Minnick was allowed to have
athletes back inside her facility. ...
Linsey Marr, 46, is a professor of
civil and environmental engineering
at Virginia Tech and joined 460 Fitness
about two years ago. She has an
expertise in airborne transmission of
viruses, air quality and nanotechnology.
“I knew the virus was transmitted
mainly through the air so I thought
it was really important to have good
ventilation so everyone wasn't able to
breathe it,” Marr told CNN. Minnick
created athlete stations near the bay
doors that gave each one 10 feet of
space, which is more than the recommended
six feet because people in the
gym would be working out and breathing
heavily.
“I did the calculations on how
big the space was, what the typical
wind speeds were in the area and if
the doors were open what would the
resulting ventilation be?” Marr said
they are now actually able to close the
doors a bit more than they initially
thought and still meet that ventilation
standard using a carbon dioxide monitor
to track indoor levels.
“Carbon dioxide is exhaled breath
and is a good indicator of how much
viruses might be building up in the
air,” Marr said. ...
Velvet Minnick, 44, is the owner
and head coach at 460 Fitness
in Blacksburg, Virginia. Like many
gym owners across the nation, she
was forced to shut down the facility
in March due to coronavirus. ... As the
state entered Phase 2 of reopening in
June, Minnick was allowed to have
athletes back inside her facility. ...
Linsey Marr, 46, is a professor of
civil and environmental engineering
at Virginia Tech and joined 460 Fitness
about two years ago. She has an
expertise in airborne transmission of
viruses, air quality and nanotechnology.
“I knew the virus was transmitted
mainly through the air so I thought
it was really important to have good
ventilation so everyone wasn't able to
breathe it,” Marr told CNN. Minnick
created athlete stations near the bay
doors that gave each one 10 feet of
space, which is more than the recommended
six feet because people in the
gym would be working out and breathing
heavily.
“I did the calculations on how
big the space was, what the typical
wind speeds were in the area and if
the doors were open what would the
resulting ventilation be?” Marr said
they are now actually able to close the
doors a bit more than they initially
thought and still meet that ventilation
standard using a carbon dioxide monitor
to track indoor levels.
“Carbon dioxide is exhaled breath
and is a good indicator of how much
viruses might be building up in the
air,” Marr said. ...
 In a year where staying indoors
has been not only encouraged but
mandated, the concept of going for a
run can seem all the less appealing.
If you’re finding it harder to motivate
yourself to get moving, you’re not
alone, but a new study has found that
even just a small amount of exercise
can make a big difference.
The research, published in the
journal Circulation, found that short
bursts of exercise could improve
health significantly by altering the
body’s level of metabolites. The paper
describes how just 12 minutes of
intense cardio can alter more than
80 percent of circulating metabolites,
which can influence a person’s cardiometabolic
and cardiovascular health
in the long run. The study looked at the levels of
588 circulating metabolites in 411
middle-aged men and women both
before and immediately after doing
12 minutes of vigorous exercise. Their
results showed favorable shifts in several
metabolites known to be linked
to heart disease, diabetes, and liver
disease. Their findings also revealed
that these benefits were influenced by
more than just their exercise routine,
as sex and measurements of body
mass were also implicated in the ratio
of metabolites.
As well as looking at the response of
individuals in real-time, the researchers
were able to predict future health ...
Read full text:
In a year where staying indoors
has been not only encouraged but
mandated, the concept of going for a
run can seem all the less appealing.
If you’re finding it harder to motivate
yourself to get moving, you’re not
alone, but a new study has found that
even just a small amount of exercise
can make a big difference.
The research, published in the
journal Circulation, found that short
bursts of exercise could improve
health significantly by altering the
body’s level of metabolites. The paper
describes how just 12 minutes of
intense cardio can alter more than
80 percent of circulating metabolites,
which can influence a person’s cardiometabolic
and cardiovascular health
in the long run. The study looked at the levels of
588 circulating metabolites in 411
middle-aged men and women both
before and immediately after doing
12 minutes of vigorous exercise. Their
results showed favorable shifts in several
metabolites known to be linked
to heart disease, diabetes, and liver
disease. Their findings also revealed
that these benefits were influenced by
more than just their exercise routine,
as sex and measurements of body
mass were also implicated in the ratio
of metabolites.
As well as looking at the response of
individuals in real-time, the researchers
were able to predict future health ...
Read full text:
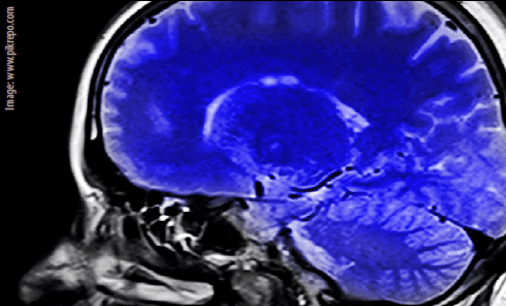 Earlier this year, a lot of people were
surprised to discover that some
people don’t have an internal monologue,
while those people who don’t were
surprised to learn other people do. Having
only ever lived in your own head,
it’s pretty weird to discover that other
people think differently than you do. ...
Shortly after everyone discovered the
other group of thinkers exist, people
started to explain to each other what
their method of thinking is like, and
how the other one is plain weird. In
one Reddit thread, user Vadermaulkylo
posted, “Today, I told my mom that I
have no internal monologue and she
stared at me like I have three heads. Is
having one common?” They confessed
they had thought it was a fictional
concept made up as a narrative device
in the TV show Dexter (about a surprisingly
teary psychopath). ...
Several people described what it’s actually
like to not have an internal monologue.
“So if your boss asks you to do
something right at the point you were
planning to leave work you don’t think
‘oh f***ing s**t b*lls what a pain? in your
head, while saying ‘No problem at all
boss,’ out loud?” one user asked. “No.
Never had that,” Vadermaulkylo responded.
“If I’m asked to do something I
don’t wanna do, I just get kinda frustrated
but that’s about it. I don’t really think
to myself.” Others confirmed their experience
was similar. ...
Earlier this year, a lot of people were
surprised to discover that some
people don’t have an internal monologue,
while those people who don’t were
surprised to learn other people do. Having
only ever lived in your own head,
it’s pretty weird to discover that other
people think differently than you do. ...
Shortly after everyone discovered the
other group of thinkers exist, people
started to explain to each other what
their method of thinking is like, and
how the other one is plain weird. In
one Reddit thread, user Vadermaulkylo
posted, “Today, I told my mom that I
have no internal monologue and she
stared at me like I have three heads. Is
having one common?” They confessed
they had thought it was a fictional
concept made up as a narrative device
in the TV show Dexter (about a surprisingly
teary psychopath). ...
Several people described what it’s actually
like to not have an internal monologue.
“So if your boss asks you to do
something right at the point you were
planning to leave work you don’t think
‘oh f***ing s**t b*lls what a pain? in your
head, while saying ‘No problem at all
boss,’ out loud?” one user asked. “No.
Never had that,” Vadermaulkylo responded.
“If I’m asked to do something I
don’t wanna do, I just get kinda frustrated
but that’s about it. I don’t really think
to myself.” Others confirmed their experience
was similar. ...
 A Korean palm oil giant has been
buying up swathes of Asia’s largest
remaining rainforests. A visual investigation
published today suggests fires
have been deliberately set on the land.
Indonesia is the world’s largest
exporter of palm oil, and Papua is its
newest frontier. The archipelago has
experienced one of the fastest rates of
deforestation in the world —vast areas
of forest have been cleared to make
way for row upon row of oil palm tree,
growing a product found in everything
from shampoo to biscuits. ...
The rich forests in the remote
province of Papua had until recently
escaped relatively untouched, but the
government is now rapidly opening
the area to investors, vowing to
bring prosperity to one of the poorest
regions in the country. Korindo [South
Korean palm oil giant] controls more
land in Papua than any other conglomerate.
The company has cleared
nearly 60,000 hectares of forests
inside its government-granted concessions
—an area the size of Chicago
or Seoul— and the company’s vast
plantation there is protected by state
security forces.
Companies like Korindo have to
clear the land in these concessions
to allow them to replant new palms.
Using fire to do that —the so-called
“slash and burn” technique— is illegal
in Indonesia due to the air pollution it
causes and the high risk blazes will get
out of control. ...
Read full text:
A Korean palm oil giant has been
buying up swathes of Asia’s largest
remaining rainforests. A visual investigation
published today suggests fires
have been deliberately set on the land.
Indonesia is the world’s largest
exporter of palm oil, and Papua is its
newest frontier. The archipelago has
experienced one of the fastest rates of
deforestation in the world —vast areas
of forest have been cleared to make
way for row upon row of oil palm tree,
growing a product found in everything
from shampoo to biscuits. ...
The rich forests in the remote
province of Papua had until recently
escaped relatively untouched, but the
government is now rapidly opening
the area to investors, vowing to
bring prosperity to one of the poorest
regions in the country. Korindo [South
Korean palm oil giant] controls more
land in Papua than any other conglomerate.
The company has cleared
nearly 60,000 hectares of forests
inside its government-granted concessions
—an area the size of Chicago
or Seoul— and the company’s vast
plantation there is protected by state
security forces.
Companies like Korindo have to
clear the land in these concessions
to allow them to replant new palms.
Using fire to do that —the so-called
“slash and burn” technique— is illegal
in Indonesia due to the air pollution it
causes and the high risk blazes will get
out of control. ...
Read full text:
 Brazil’s mining authority is actively
entertaining more than 3,000
requests to mine on Indigenous lands
in the Amazon, despite such activity
being prohibited under the country’s
Constitution, an investigation by the
InfoAmazonia project has found.
The “Mined Amazon” investigation
uncovered dozens of applications being
filed with the National Mining Agency
(ANM) every year, with the agency
keeping them on file and not rejecting
them immediately as it is obliged to do.
Even the economic slowdown prompted
by the COVID-19 pandemic hasn’t
stemmed the tide of mining requests.
More than 38,000 Indigenous people
have been infected since the start of
the health emergency, with 867 dead,
according to the Articulation of Brazilian
Indigenous Peoples (APIB). Yet
throughout 2020, 145 mining applications
have been recorded —the highest
number in 24 years.
The lands of the Kayapó people in
the state of Pará are the most affected,
targeted by more than a third of applications
this year.
Interest in mining on Indigenous territories
has grown under the administration
of President Jair Bolsonaro. In
the two years before he took office at
the start of 2019, the number of such
mining requests averaged 50 per year;
since then, the annual average has
spiked to 117. ...
Read full text:
Brazil’s mining authority is actively
entertaining more than 3,000
requests to mine on Indigenous lands
in the Amazon, despite such activity
being prohibited under the country’s
Constitution, an investigation by the
InfoAmazonia project has found.
The “Mined Amazon” investigation
uncovered dozens of applications being
filed with the National Mining Agency
(ANM) every year, with the agency
keeping them on file and not rejecting
them immediately as it is obliged to do.
Even the economic slowdown prompted
by the COVID-19 pandemic hasn’t
stemmed the tide of mining requests.
More than 38,000 Indigenous people
have been infected since the start of
the health emergency, with 867 dead,
according to the Articulation of Brazilian
Indigenous Peoples (APIB). Yet
throughout 2020, 145 mining applications
have been recorded —the highest
number in 24 years.
The lands of the Kayapó people in
the state of Pará are the most affected,
targeted by more than a third of applications
this year.
Interest in mining on Indigenous territories
has grown under the administration
of President Jair Bolsonaro. In
the two years before he took office at
the start of 2019, the number of such
mining requests averaged 50 per year;
since then, the annual average has
spiked to 117. ...
Read full text:
 Neurodiverse means having a brain
that’s wired differently. This sector
of the population faces a plethora of discrimination
in the workplace. According
to Danielle Pavliv, manager of diversity
and inclusion for SAS, over 80% of
people with Autism Spectrum Disorder
(ASD) are under or unemployed although
nearly 62.6% of autistic individuals have
some exceptional talent or ability –not
always, but often technical skills.
Analytics software company SAS is
on a mission to bring more of these
people into the fold and provide them
with opportunities to utilize their
talents fully. This strategy serves both
parties well. Here’s why: The Smithsonian
Science Education Center
predicted that in 2018, 2.5 Million US
STEM jobs would go unfilled. ...
UX design intern and future fulltime
employee, Chris Rackley, applied
and was accepted into the SAS intern
program for students with ASD. ...
“The interview process was stressful
for me at most companies. ... I, along
with many people on the AS, have
difficulty with auditory processing. I
never received a return call from any
of the companies that interviewed me
over the speaker.” Rackley believes
this is one of the reasons individuals
on the AS are underemployed.
They cannot get through the typical
hiring process. ...
Read full text:
Neurodiverse means having a brain
that’s wired differently. This sector
of the population faces a plethora of discrimination
in the workplace. According
to Danielle Pavliv, manager of diversity
and inclusion for SAS, over 80% of
people with Autism Spectrum Disorder
(ASD) are under or unemployed although
nearly 62.6% of autistic individuals have
some exceptional talent or ability –not
always, but often technical skills.
Analytics software company SAS is
on a mission to bring more of these
people into the fold and provide them
with opportunities to utilize their
talents fully. This strategy serves both
parties well. Here’s why: The Smithsonian
Science Education Center
predicted that in 2018, 2.5 Million US
STEM jobs would go unfilled. ...
UX design intern and future fulltime
employee, Chris Rackley, applied
and was accepted into the SAS intern
program for students with ASD. ...
“The interview process was stressful
for me at most companies. ... I, along
with many people on the AS, have
difficulty with auditory processing. I
never received a return call from any
of the companies that interviewed me
over the speaker.” Rackley believes
this is one of the reasons individuals
on the AS are underemployed.
They cannot get through the typical
hiring process. ...
Read full text:
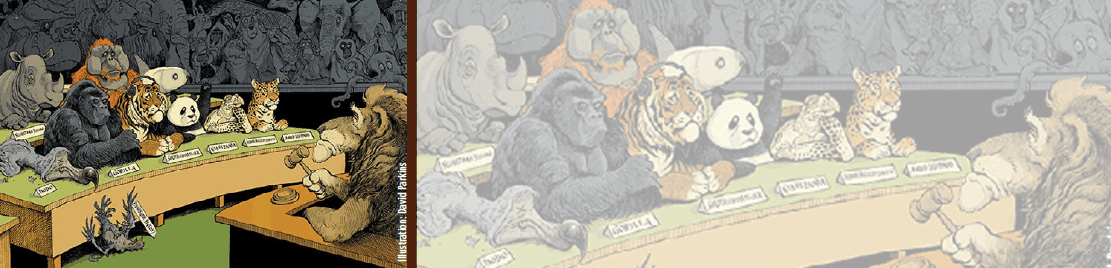
 Eleven Tasmanian devils have been
reintroduced to mainland Australia,
more than 3,000 years after they died
out there. The carnivorous marsupials
have been released into a 400-hectare
(988-acre) wildlife sanctuary north of
Sydney, New South Wales, Australian
NGO Aussie Ark said in a statement.
“In 100 years, we are going to be
looking back at this day as the day that
set in motion the ecological restoration
of an entire country,” said Tim
Faulkner, president of Aussie Ark.
“Not only is this the reintroduction
of one of Australia’s beloved animals,
but of an animal that will engineer the
entire environment around it, restoring
and rebalancing our forest ecology after centuries of devastation from
introduced foxes and cats and other
invasive predators.”
Tasmanian devils died out on the
mainland after the arrival of dingoes
and were restricted to the island of
Tasmania. However, their numbers suffered
another blow from a contagious
form of cancer known as Devil Facial
Tumor Disease (DFTD), which has killed
around 90% of the population since it
was discovered in 1996. There are now
just 25,000 wild devils left in Tasmania,
and Aussie Ark has been working
to conserve the species for the past 10
years. ...
Read full text and watch video:
Eleven Tasmanian devils have been
reintroduced to mainland Australia,
more than 3,000 years after they died
out there. The carnivorous marsupials
have been released into a 400-hectare
(988-acre) wildlife sanctuary north of
Sydney, New South Wales, Australian
NGO Aussie Ark said in a statement.
“In 100 years, we are going to be
looking back at this day as the day that
set in motion the ecological restoration
of an entire country,” said Tim
Faulkner, president of Aussie Ark.
“Not only is this the reintroduction
of one of Australia’s beloved animals,
but of an animal that will engineer the
entire environment around it, restoring
and rebalancing our forest ecology after centuries of devastation from
introduced foxes and cats and other
invasive predators.”
Tasmanian devils died out on the
mainland after the arrival of dingoes
and were restricted to the island of
Tasmania. However, their numbers suffered
another blow from a contagious
form of cancer known as Devil Facial
Tumor Disease (DFTD), which has killed
around 90% of the population since it
was discovered in 1996. There are now
just 25,000 wild devils left in Tasmania,
and Aussie Ark has been working
to conserve the species for the past 10
years. ...
Read full text and watch video:
 Advent
candle
holder
(34 x 24 cm).
www.bengt-lotta.se
Advent
candle
holder
(34 x 24 cm).
www.bengt-lotta.se
 Wear them just like
glasses, with an ultra lightweight design
that sits comfortably on the face and
feature an all-over UVA and UVB coating.
All Vue Shields have anti-fog coatings to
minimize the impact of climate conditions.
www.vueshield.com
Wear them just like
glasses, with an ultra lightweight design
that sits comfortably on the face and
feature an all-over UVA and UVB coating.
All Vue Shields have anti-fog coatings to
minimize the impact of climate conditions.
www.vueshield.com
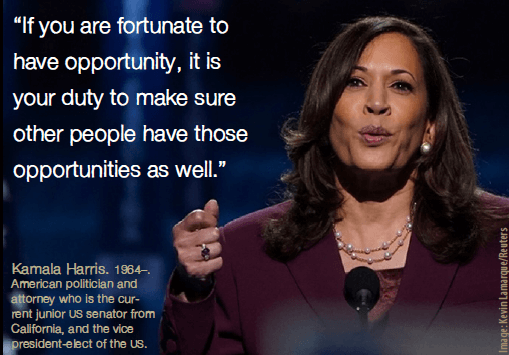 “If you are fortunate to
have opportunity, it is
your duty to make sure
other people have those
opportunities as well.”
“If you are fortunate to
have opportunity, it is
your duty to make sure
other people have those
opportunities as well.”
 The Master of Sociology (MA, MS)
program objective is to help students
develop professionally by employing
analytical and research skills
through the use of research methods,
research experience, and analytical
skills necessary for the employment in
government, nonprofit, and corporate
organizations. The Master of Sociology
program is offered online via
distance learning. After evaluating
both academic record and life experience,
AIU staff working in conjunction
with Faculty and Academic Advisors
will assist students in setting up a
custom-made program, designed on
an individual basis. This flexibility to
meet student needs is seldom found
in other distance learning programs.
Our online program does not require
all students to take the same subjects/
courses, use the same books, or
learning materials. Instead, the online
Master of Sociology curriculum is
designed individually by the student
and academic advisor. It specifically
addresses strengths and weaknesses
with respect to market opportunities
in the student’s major and intended
field of work.
Understanding that industry and
geographic factors should influence
the content of the curriculum instead
of a standardized one-fits-all design is
the hallmark of AIU’s unique approach
to adult education. This philosophy
addresses the dynamic and constantly
changing environment of working professionals
by helping adult students in
reaching their professional and personal
goals within the scope of the program.
The Master of Sociology (MA, MS)
program objective is to help students
develop professionally by employing
analytical and research skills
through the use of research methods,
research experience, and analytical
skills necessary for the employment in
government, nonprofit, and corporate
organizations. The Master of Sociology
program is offered online via
distance learning. After evaluating
both academic record and life experience,
AIU staff working in conjunction
with Faculty and Academic Advisors
will assist students in setting up a
custom-made program, designed on
an individual basis. This flexibility to
meet student needs is seldom found
in other distance learning programs.
Our online program does not require
all students to take the same subjects/
courses, use the same books, or
learning materials. Instead, the online
Master of Sociology curriculum is
designed individually by the student
and academic advisor. It specifically
addresses strengths and weaknesses
with respect to market opportunities
in the student’s major and intended
field of work.
Understanding that industry and
geographic factors should influence
the content of the curriculum instead
of a standardized one-fits-all design is
the hallmark of AIU’s unique approach
to adult education. This philosophy
addresses the dynamic and constantly
changing environment of working professionals
by helping adult students in
reaching their professional and personal
goals within the scope of the program.
 Atlantic International University is accredited by the Accreditation Service for International
Schools, Colleges and Universities (ASIC). ASIC Accreditation is an internationally
renowned quality standard for colleges and universities. Visit ASIC’s Directory of Accredited
Colleges and Universities. ASIC is a member of CHEA International Quality Group
(CIQG) in the USA, an approved accreditation body by the Ministerial Department of the Home Office
in the UK, and is listed in the International Directory of the Council for Higher Education Accreditation
(CHEA). The University is based in the United States and was established by corporate charter in 1998.
Atlantic International University is accredited by the Accreditation Service for International
Schools, Colleges and Universities (ASIC). ASIC Accreditation is an internationally
renowned quality standard for colleges and universities. Visit ASIC’s Directory of Accredited
Colleges and Universities. ASIC is a member of CHEA International Quality Group
(CIQG) in the USA, an approved accreditation body by the Ministerial Department of the Home Office
in the UK, and is listed in the International Directory of the Council for Higher Education Accreditation
(CHEA). The University is based in the United States and was established by corporate charter in 1998.
 In some cases, accredited colleges
may not accept for transfer courses and degrees
completed at unaccredited colleges, and some
employers may require an accredited degree as
a basis for eligibility for employment. Potential
students should consider how the above may affect
their interests, AIU respects the unique rules and
regulations of each country and does not seek to
influence the respective authorities. In the event
that a prospective student wishes to carry out any
government review or process in regards to his
university degree, we recommend that the requirements
of such are explored in detail with the relevant
authorities by the prospective student as the
university does not intervene in such processes.
AIU students can be found in over 180 countries,
they actively participate and volunteer
in their communities as part of their academic
program and have allocated thousands of service
hours to diverse causes and initiatives. AIU
programs follow the standards commonly used by
colleges and universities in the United States with
regards to the following: academic program
structure, degree issued, transcript, and
other graduation documents.
AIU graduation documents can include
an apostille and authentication from the
US Department of State to facilitate their
use internationally.
In some cases, accredited colleges
may not accept for transfer courses and degrees
completed at unaccredited colleges, and some
employers may require an accredited degree as
a basis for eligibility for employment. Potential
students should consider how the above may affect
their interests, AIU respects the unique rules and
regulations of each country and does not seek to
influence the respective authorities. In the event
that a prospective student wishes to carry out any
government review or process in regards to his
university degree, we recommend that the requirements
of such are explored in detail with the relevant
authorities by the prospective student as the
university does not intervene in such processes.
AIU students can be found in over 180 countries,
they actively participate and volunteer
in their communities as part of their academic
program and have allocated thousands of service
hours to diverse causes and initiatives. AIU
programs follow the standards commonly used by
colleges and universities in the United States with
regards to the following: academic program
structure, degree issued, transcript, and
other graduation documents.
AIU graduation documents can include
an apostille and authentication from the
US Department of State to facilitate their
use internationally.
| Dr. Franklin Valcin President/Academic Dean |
Dr. José Mercado Chief Executive Officer Chairman of the Board of Trustees |
Ricardo González, PhD Provost |
| Dr. Ricardo Gonzalez Chief Operation Officer and MKT Director |
Linda Collazo Logistics Coordinator |
Dr. Silvia Restorff Academic Advisor |
| Dr. Miriam Garibaldi Viceprovost for Research |
Irina Ivashuk Alumni Association Coordinator |
Dr. Prakash Menon Academic Advisor |
| Dr. Ofelia Miller Director of AIU |
Clara Margalef Director of Special Projects of AIU |
Carlos Aponte Telecommunications Coordinator |
| Juan Pablo Moreno Director of Operations |
David Jung Corporate/Legal Counsel |
Dr. Nilani Ljunggren De Silva Academic Advisor |
| Paula Viera Director of Intelligence Systems |
Bruce Kim Advisor/Consultant |
Dr. Scott Wilson Academic Advisor |
| Felipe Gomez Design Director / IT Supervisor |
Thomas Kim Corporate/ Accounting Counsel |
Dr. Mohammad Shaidul Islam Academic Advisor |
| Daritza Ysla IT Coordinator |
Camila Correa Quality Assurance Coordinator |
Dr. Edgar Colon Academic Advisor |
| Nadeem Awan Chief Programming Officer |
Maricela Esparza Administrative Coordinator |
Deborah Rodriguez Academic Tutor Coordinator |
| Dr. Jack Rosenzweig Dean of Academic Affairs |
Chris Benjamin IT and Hosting Support |
Cyndy Dominguez Academic Tutor Coordinator |
| Dr. Edward Lambert Academic Director |
Mayra Bolivar Accounting Coordinator |
Kinmberly Diaz Admissions Support Tutor |
| Dr. Ariadna Romero Advisor Coordinator |
Roberto Aldrett Communications Coordinator |
Amalia Aldrett Admissions Coordinator |
| Nadia Gabaldon Academic Coordinator |
Giovanni Castillo IT Support |
Sandra Garcia Admissions Coordinator |
| Jhanzaib Awan Senior Programmer |
Jaime Rotlewicz Dean of Admissions |
Jose Neuhaus Admissions Support |
| Leonardo Salas Human Resource Manager |
Dr. Mario Rios Academic Advisor |
Junko Shimizu Admissions Coordinator |
| Benjamin Joseph IT and Technology Support |
Michael Phillips Registrar’s Office |
Veronica Amuz Admissions Coordinator |
| Rosie Perez Finance Coordinator |
Rene Cordon Admissions Support |
Alba Ochoa Admissions Coordinator |
| Chris Soto Admissions Counselor |
Jenis Garcia Admissions Counselor |
|
 The School of Business and Economics
allows aspiring and practicing
professionals, managers, and entrepreneurs
in the private and public sectors
to complete a self paced distance
learning degree program of the highest
academic standard.
The ultimate goal is to empower
learners and help them take advantage
of the enormous array of resources
from the world environment in order
to eliminate the current continuum of
poverty and limitations.
Degree programs are designed for
those students whose professional experience has been in business,
marketing, administration, economics,
finance and management.
The School of Business and Economics
allows aspiring and practicing
professionals, managers, and entrepreneurs
in the private and public sectors
to complete a self paced distance
learning degree program of the highest
academic standard.
The ultimate goal is to empower
learners and help them take advantage
of the enormous array of resources
from the world environment in order
to eliminate the current continuum of
poverty and limitations.
Degree programs are designed for
those students whose professional experience has been in business,
marketing, administration, economics,
finance and management.
 The School of Social and Human Studies
is focused on to the development of
studies which instill a core commitment
to building a society based on social and
economic justice and enhancing opportunities
for human well being.
The founding principles lie on the
basic right of education as outlined
in the Declaration of Human Rights.
We instill in our students a sense of
confidence and self reliance in their
ability to access the vast opportunities
available through information channels,
the world wide web, private, public,
nonprofit, and nongovernmental organizations in an ever expanding
global community.
Degree programs are aimed towards
those whose professional life has been
related to social and human behavior,
with the arts, or with cultural studies.
The School of Social and Human Studies
is focused on to the development of
studies which instill a core commitment
to building a society based on social and
economic justice and enhancing opportunities
for human well being.
The founding principles lie on the
basic right of education as outlined
in the Declaration of Human Rights.
We instill in our students a sense of
confidence and self reliance in their
ability to access the vast opportunities
available through information channels,
the world wide web, private, public,
nonprofit, and nongovernmental organizations in an ever expanding
global community.
Degree programs are aimed towards
those whose professional life has been
related to social and human behavior,
with the arts, or with cultural studies.
 The School of Science and Engineering
seeks to provide dynamic, integrated,
and challenging degree programs
designed for those whose experience
is in industrial research, scientific production,
engineering and the general
sciences. Our system for research and
education will keep us apace with the
twenty-first century reach scientific
advance in an environmentally and
ecologically responsible manner to allow
for the sustainability of the human
population. We will foster among our
students a demand for ethical behavior,
an appreciation for diversity, an understanding
of scientific investigation, knowledge of design innovation, a
critical appreciation for the importance
of technology and technological change
for the advancement of humanity.
The School of Science and Engineering
seeks to provide dynamic, integrated,
and challenging degree programs
designed for those whose experience
is in industrial research, scientific production,
engineering and the general
sciences. Our system for research and
education will keep us apace with the
twenty-first century reach scientific
advance in an environmentally and
ecologically responsible manner to allow
for the sustainability of the human
population. We will foster among our
students a demand for ethical behavior,
an appreciation for diversity, an understanding
of scientific investigation, knowledge of design innovation, a
critical appreciation for the importance
of technology and technological change
for the advancement of humanity.
 With access to a global catalog created and maintained collectively by more than
9,000 participating institutions, AIU students have secured excellent research
tools for their study programs.
With access to a global catalog created and maintained collectively by more than
9,000 participating institutions, AIU students have secured excellent research
tools for their study programs.